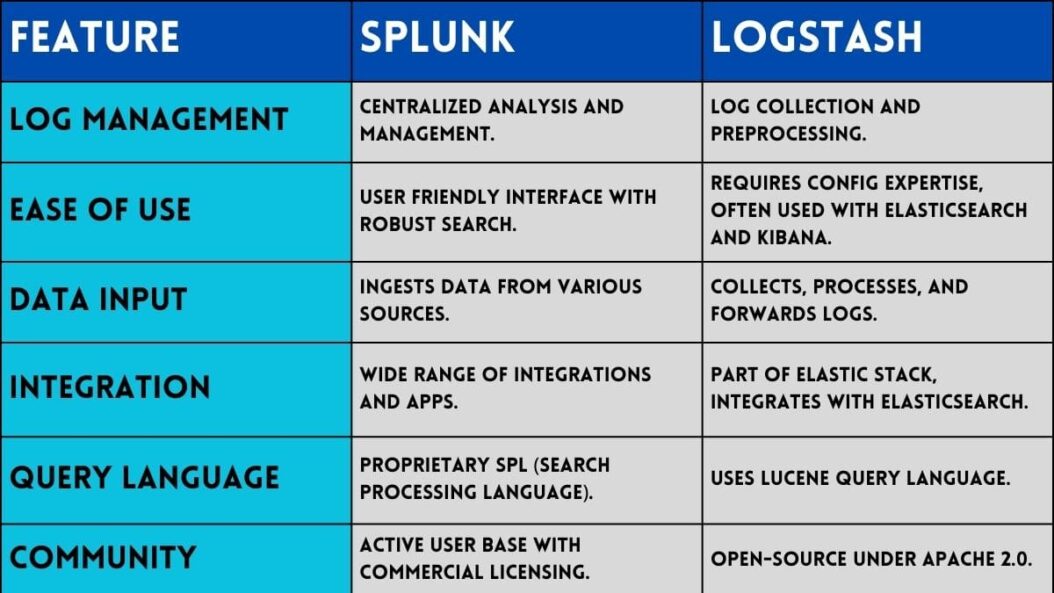
Splunk and Logstash are both popular log management and analysis tools. But which one is better for your needs? This comprehensive comparison examines the key differences between Splunk and Logstash to help you decide.
What is Splunk?
Splunk is a commercial log management and analysis software. It collects, indexes, and enables you to search machine generated big data from websites, applications, sensors, devices, and other IT infrastructure components.
Key capabilities include:
- Real time reporting and dashboards
- Ad hoc searching to troubleshoot issues
- Data visualization and analysis
- Alerting based on set thresholds
Splunk makes it easy to analyze and gain operational intelligence from machine data. It has an intuitive interface and works across on-premises, cloud, and hybrid environments.
What is Logstash?
Logstash is an open source tool for managing events and logs. It collects, transforms, and transports log data.
Key tasks include:
- Collecting logs and event data from various sources
- Parsing and transforming the data into a consistent format
- Routing the data to various outputs including Elasticsearch
As part of the ELK (Elasticsearch, Logstash, Kibana) stack, Logstash prepares logs for analysis in Elasticsearch. It enriches log data with extra metadata to facilitate searching.
Splunk vs Logstash: Comparision
Data Sources
Splunk
Splunk can collect and index data from most sources including:
- Files and directories
- Windows event logs
- Network traffic
- Configuration files
- System metrics
- Web servers
- Applications
- Social media APIs
- Cloud services
- It uses universal forwarders and lightweight forwarders.
Logstash
Logstash can ingest data from over 200+ sources such as:
- Files
- Syslogs
- Web servers
- Databases
- Cloud services
- APIs
- MQ servers
- Docker containers
- It has a range of input plugins.
Verdict
Splunk and Logstash support most common data sources. Splunk has broader cloud service support whereas Logstash is better for containers.
Data Processing
Splunk
Splunk indexes data in a proprietary structure optimized for fast searching. It uses machine learning to parse unstructured data. You can enrich data with lookup files and metadata.
Logstash
Logstash has filters to parse, transform, enrich, and manipulate event data. You can route data to various outputs after processing. It uses Grok patterns to structure unstructured logs.
Verdict
Splunk has better capabilities to handle unstructured data out of the box. But Logstash gives more control over parsing and manipulating data.
Searching and Analysis
Splunk
Splunk provides powerful ad hoc searching and pivoting functionality with stats commands. Its dashboards and visualizations make it easy to analyze trends. Splunk also has statistical language models and ML algorithms.
Logstash
Logstash sends data to Elasticsearch where you analyze it with Kibana. Kibana provides data discovery, visualizations, dashboards, and robust searching. It leverages Elasticsearch for analytics.
Verdict
Splunk has built in analytics whereas Logstash relies on the ELK stack. Splunk makes it easier to get started with searching and reporting.
Alerting
Splunk
Splunk can trigger alerts based on real time data or historical trends. It lets you set thresholds and conditions for triggering actions like emails, script execution, etc.
Logstash
You need to use additional ELK stack components like Elastalert for complex alerting. But Logstash has some limited alerting support via certain outputs.
Verdict
Splunk has much more advanced and customizable alerting capabilities out of the box.
Scalability and Performance
Splunk
Splunk utilizes a distributed search architecture to handle high data volumes and user loads. You can add indexers and search heads to scale as needed. It offers high ingestion speeds and fast search performance even on TBs+ of data.
Logstash
Since Logstash streams events to Elasticsearch in real time, you can scale by adding more Elasticsearch nodes. Logstash throughput can reach millions of events per second. It leverages Elasticsearch for distributed processing.
Verdict
Both Splunk and the ELK stack allow scaling to any data volume. Splunk may have an edge in enterprise wide deployments.
Management and Admin
Splunk
Splunk provides centralized management via its interface. You can manage configurations, users, permissions, apps, alerts, and more across distributed environments. It has built-in UI dashboards.
Logstash
You use Kibana for admin tasks like user management, system monitoring, and Logstash pipeline configuration. But some advanced settings require command line usage. Management requires using multiple ELK components.
Verdict
Splunk offers slightly easier admin workflows from a single interface. But Logstash provides flexibility.
Pricing and Support
Splunk
Splunk offers premium support services but at a high cost with complex pricing tiers based on volume. Licenses, pricing, and support are less flexible.
Logstash
Logstash and Elasticsearch are free open source tools but offer community based support only. Extended support from Elastic is paid. You get more flexibility and lower costs.
Verdict
Logstash is far more budget friendly, avoiding vendor lock-in. But Splunk offers robust enterprise grade support.
Use Cases
Splunk
Typical use cases where Splunk excels:
- IT operations analytics
- Security monitoring and analysis
- Business analytics
- Application management
- Cloud monitoring
Its breadth of data source and analytics support make it suitable for most use cases. Integrations with cloud platforms like AWS, Azure, and GCP enable various observability workflows.
Logstash
Common Logstash use cases:
- Centralized logging pipeline
- Streaming integration hub
- Parsing multidimensional data
- Powering analytics in Elasticsearch
- Gathering metrics for monitoring
- Cloud scale log processing
As a log shipper and aggregator, Logstash fits well for streaming data pipelines and feeding into the ELK stack.
Conclusion
Splunk and Logstash both help make sense of machine data but with different approaches. Splunk is an end to end commercial solution designed specifically for data analytics and operations intelligence. It focuses more on faster time to insight across a broader set of data sources. Logstash performs well as an open source data collection and processing pipeline to prepare data for Elasticsearch. It provides more flexibility for custom data workflows.
Ultimately, Splunk is the easiest way to get started with log management and analysis using a pre built toolset. But Logstash allows creating more customized logging pipelines at scale while avoiding vendor lock-in. Evaluate your use case, data sources, budget, and app ecosystem to determine if Splunk or Logstash is a better fit. In some cases, using both together can be beneficial.
FAQs
Can Splunk and Logstash work together?
Yes, it’s common to use Splunk to collect and analyze data while also using Logstash to ship a subset of data to Elasticsearch for longer term storage or other purposes. They can complement each other in some architectures.
Is Splunk easier to use than Logstash?
Generally yes since Splunk provides an end to end solution with visual interfaces out of the box. You avoid needing to set up multiple components like with Logstash, Elasticsearch, and Kibana.
Does Splunk replace Logstash?
Not directly. Splunk specializes more in analytics and visibility whereas Logstash focuses on building automated data pipelines. Logstash also feeds data to Elasticsearch for further analytics. They have slightly different core competencies so often complement rather than replace.
Can Logstash match Splunk’s data processing capabilities?
Logstash itself has less built in intelligence for parsing and enriching data. But when combined with Elasticsearch, Logstash provides a scalable solution for crunching large amounts of data for analytics, rivaling much of Splunk’s power.
Is Logstash cheaper than Splunk?
Definitely. Since Logstash is open source, you only pay for support subscriptions which are less costly than Splunk’s licenses. Overall TCO is lower, avoiding vendor lock-in. But the ELK stack may require more effort to deploy and manage.
- How to Enable Screen Sharing in Discord? – Guide - April 19, 2026
- How to Share Internet from Mobile to Mobile without Hotspot? - April 19, 2026
- 12 Best Janitor.Ai Alternatives (FREE) - April 18, 2026
